IT Security Management: Difference between revisions
No edit summary |
No edit summary |
||
| Line 1: | Line 1: | ||
< | <itpmch><title>IT Security Management | IT Process Wiki</title> | ||
<meta name="keywords" content="information security management, itil security management, security management itil, itil security management process, security management process" /> | |||
<meta name="description" content="Information Security Management: ITIL process definition - Sub-processes - Terms - Additional information on Information Security Management." /> | |||
</itpmch> | |||
<imagemap> | <imagemap> | ||
Image:ITIL-Wiki-de-es.jpg|DE - ES - Information Security Management|100px | Image:ITIL-Wiki-de-es.jpg|DE - ES - Information Security Management|100px | ||
| Line 8: | Line 11: | ||
<br style="clear:both;"/> | <br style="clear:both;"/> | ||
<p> </p> | <p> </p> | ||
'''<span id="Overview">Objective:</span>''' <html><span itemprop="description"><i | '''<span id="Overview">Objective:</span>''' <html><span id="md-webpage-description" itemprop="description"><i>Information Security Management</i> aims to ensure the confidentiality, integrity and availability of an organization's information, data and IT services. ITIL Security Management usually forms part of an organizational approach to security management which has a wider scope than the IT Service Provider.</span></p> | ||
<p><b>Part of</b>: <a | <p><b>Part of</b>: <a href="https://wiki.en.it-processmaps.com/index.php/ITIL_Service_Design" title="ITIL Service Design">Service Design</a></html> | ||
'''Process Owner''': [[IT Security Management#Information Security Manager|Information Security Manager]] | '''Process Owner''': [[IT Security Management#Information Security Manager|Information Security Manager]] | ||
| Line 21: | Line 23: | ||
ITIL V3 treats Information Security Management as part of the Service Design core volume, resulting in a better integration of this process into the Service Lifecycle (the previous ITIL version provided guidance on Security Management in a separate book). | ITIL V3 treats Information Security Management as part of the Service Design core volume, resulting in a better integration of this process into the Service Lifecycle (the previous ITIL version provided guidance on Security Management in a separate book). | ||
[[Image:Itil-security-management.jpg|right|thumb|375px|alt=Information Security Management ITIL|[https://wiki.en.it-processmaps.com/images/pdf/process_overview_it_security_management_itilv3.pdf ITIL Security Management]]] | [[Image:Itil-security-management.jpg|right|thumb|375px|alt=Information Security Management ITIL|link=https://wiki.en.it-processmaps.com/index.php/File:Itil-security-management.jpg|[https://wiki.en.it-processmaps.com/images/pdf/process_overview_it_security_management_itilv3.pdf ITIL Security Management]]] | ||
The process was updated to account for new information security concerns. | The process was updated to account for new information security concerns. | ||
| Line 117: | Line 119: | ||
==KPIs== | ==KPIs== | ||
<html><ul><li><a href="https://wiki.en.it-processmaps.com/index.php/ITIL_KPIs_Service_Design#ITIL_KPIs_Information_Security_Management" title="ITIL KPIs Security Management">Key Performance Indicators (KPIs) Information Security Management</a></li></ul> | |||
<p></html> | |||
<p> </p> | <p> </p> | ||
| Line 184: | Line 186: | ||
<span id="ITIL Security Roles">[3] siehe [[ITIL Roles|→ Role descriptions ...]]</span> | <span id="ITIL Security Roles">[3] siehe [[ITIL Roles|→ Role descriptions ...]]</span> | ||
<p> </p> | <p> </p> | ||
== | ==Notes== | ||
<html> | <html>By:  Stefan Kempter <a rel="author" href="https://plus.google.com/111925560448291102517/about"><img style="margin:0px 0px 0px 0px;" src="/skins/Vector/images/itpm/bookmarking/gplus.png" width="16" height="16" title="By: Stefan Kempter | Profile on Google+" alt="Author: Stefan Kempter, IT Process Maps GbR" /></a>, IT Process Maps.</p> | ||
<p> </p> | |||
< | |||
</ | |||
<p><small> | <p><small> | ||
| Line 222: | Line 208: | ||
</span> | </span> | ||
</small></p> | </small></p> | ||
</ | |||
<!-- define schema.org/WebPage --> <span itemscope itemtype="https://schema.org/WebPage" itemref="md-webpage-description"> | |||
<meta itemprop="name" content="Information Security Management" /> | |||
<meta itemprop="alternativeHeadline" content="ITIL Security Management" /> | |||
<meta itemprop="significantLinks" content="https://wiki.en.it-processmaps.com/index.php/ITIL_KPIs_Service_Design#ITIL_KPIs_Information_Security_Management" /> | |||
<link itemprop="url" href="https://wiki.en.it-processmaps.com/index.php/IT_Security_Management" /> | |||
<meta itemprop="inLanguage" content="en" /> | |||
<link itemprop="citation" href="https://wiki.de.it-processmaps.com/index.php/IT_Security_Management" /> | |||
<link itemprop="citation" href="https://wiki.es.it-processmaps.com/index.php/ITIL_Gestion_de_la_Seguridad_de_TI" /> | |||
<meta itemprop="Headline" content="IT Security Management" /> | |||
<link itemprop="isPartOf" href="https://wiki.en.it-processmaps.com/index.php/ITIL_Service_Design" /> | |||
<link itemprop="primaryImageOfPage" href="https://wiki.en.it-processmaps.com/images/e/e7/Itil-security-management.jpg" /> | |||
<link itemprop="author" href="https://plus.google.com/111925560448291102517/about" /> | |||
<meta itemprop="author" content="Stefan Kempter" /> | |||
<meta itemprop="creator copyrightHolder publisher" content="IT Process Maps" /> | |||
</span><p></html> | |||
<!-- This page is assigned to the following categories: --> | <!-- This page is assigned to the following categories: --> | ||
[[Category:ITIL V3]][[Category:ITIL 2011]][[Category:ITIL process]][[Category:Service Design|Information Security Management]][[Category:Information Security Management|!]] | [[Category:ITIL V3]][[Category:ITIL 2011]][[Category:ITIL process]][[Category:Service Design|Information Security Management]][[Category:Information Security Management|!]] | ||
<!-- --- --> | <!-- --- --> | ||
Revision as of 14:29, 15 May 2016

Objective: Information Security Management aims to ensure the confidentiality, integrity and availability of an organization's information, data and IT services. ITIL Security Management usually forms part of an organizational approach to security management which has a wider scope than the IT Service Provider.
Part of: Service Design
Process Owner: Information Security Manager
Process Description
ITIL V3 treats Information Security Management as part of the Service Design core volume, resulting in a better integration of this process into the Service Lifecycle (the previous ITIL version provided guidance on Security Management in a separate book).
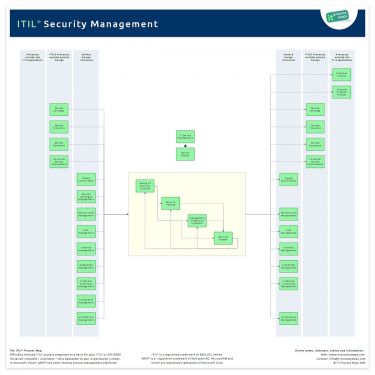
The process was updated to account for new information security concerns.
ITIL does not provide a detailed explanation of all aspects of Information Security Management, as there are dedicated and more detailed standards available (see, for example, ISO 27001). Rather, ITIL highlights the most important activities and assists in identifying interfaces with other Service Management processes.
Following the introduction of Design Coordination in ITIL 2011 the information flows have been adapted. The process overview of ITIL Security Management (.JPG) is showing the most important interfaces (see Figure 1).
Sub-Processes
These are the Information Management sub-processes and their process objectives:
Design of Security Controls
- Process Objective: To design appropriate technical and organizational measures in order to ensure the confidentiality, integrity, security and availability of an organization's assets, information, data and services.
Security Testing
- Process Objective: To make sure that all security mechanisms are subject to regular testing.
Management of Security Incidents
- Process Objective: To detect and fight attacks and intrusions, and to minimize the damage incurred by security breaches.
Security Review
- Process Objective: To review if security measures and procedures are still in line with risk perceptions from the business side, and to verify if those measures and procedures are regularly maintained and tested.
Definitions
The following ITIL terms and acronyms (information objects) are used in the Security Management process to represent process outputs and inputs:
Availability/ ITSCM/ Security Testing Schedule
- A schedule for the regular testing of all availability, continuity and security mechanisms, jointly maintained by Availability, IT Service Continuity and Information Security Management.
Event Filtering and Correlation Rules
- Rules and criteria used to determine if an Event is significant and to decide upon an appropriate response. Event Filtering and Correlation Rules are typically used by Event Monitoring systems. Some of those rules are defined during the Service Design stage, for example to ensure that Events are triggered when the required service availability is endangered.
- Note: The output "Event Filtering and Correlation Rules" has been added in ITIL 2011, to emphasize that (some) Event filtering and correlation rules should be designed by Information Security Management to support the detection of security issues.
Information Security Policy
- The Information Security Management Policy describes and communicates the organization's approach to managing information security. It includes references to more specific Underpinning Information Security Policies which, for example, set binding rules for the use of systems and information.
Information Security Report
- The Information Security Report provides other Service Management processes and IT Management with information related to Information Security issues.
Security Advisories
- A list of known security vulnerabilities compiled from input by third-party product suppliers. The list contains instructions for preventive measures and for the handling of security breaches once they occur.
Security Alert
- A warning produced by Information Security Management, typically released when outbreaks of security threats are foreseeable or already under way. The aim is to make sure that users and IT staff are able to identify any attacks and take appropriate precautions.
Security Management Information System (SMIS)
- A virtual repository of all Information Security Management data, usually stored in multiple physical locations.
Test Report
- A Test Report provides a summary of testing and assessment activities. A Test Report is created for example during Release tests in the Service Transition stage or during tests carried out by Availability, IT Service Continuity or Information Security Management.
Underpinning Information Security Policy
- Underpinning Information Security Policies are specific policies complementing the main Information Security Policy by setting binding rules for the use of systems and information as well as for the use and delivery of services, with the aim of improving information security.
KPIs
Roles | Responsibilities
Information Security Manager - Process Owner
- The Information Security Manager is responsible for ensuring the confidentiality, integrity and availability of an organization’s assets, information, data and IT services. He is usually involved in an organizational approach to Security Management which has a wider scope than the IT service provider, and includes handling of paper, building access, phone calls etc., for the entire organization.
| Responsibility Matrix: ITIL Security Management | ||||||
| ITIL Role | Sub-Process | Information Security Manager | Service Owner[3] | Applications Analyst[3] | Technical Analyst[3] | IT Operator[3] | Facilities Manager[3] |
|---|---|---|---|---|---|---|
| Design of Security Controls | A[1]R[2] | R | R | R | - | - |
| Security Testing | AR | - | - | - | R | R |
| Management of Security Incidents | AR | - | - | - | - | - |
| Security Review | AR | - | - | - | - | - |
Remarks
[1] A: Accountable according to the RACI Model: Those who are ultimately accountable for the correct and thorough completion of the Information Security Management process.
[2] R: Responsible according to the RACI Model: Those who do the work to achieve a task within ITIL Security Management.
[3] siehe → Role descriptions ...
Notes
By: Stefan Kempter ![]() , IT Process Maps.
, IT Process Maps.
Process Description › Sub-Processes › Definitions › Roles